Public WiFi over HSCN Access Circuits
This Health and Social Care Network (HSCN) public Wi-Fi over HSCN guide will assist in understanding and decision making when providing public Wi-Fi over HSCN access circuits.
Introduction
To meet various business needs and other obligations, many NHS organisations have procured separate connectivity for HSCN and public Wi-Fi traffic.
These separate products are often from the same single supplier and connect to common infrastructure elements within the supplier’s network and the site’s network.
The HSCN Obligations Framework has been extended to allow for the HSCN access circuit to be used to carry the public Wi-Fi traffic without risk to business functionality, if suitable controls are put in place to prioritise and protect business traffic.
Options overview
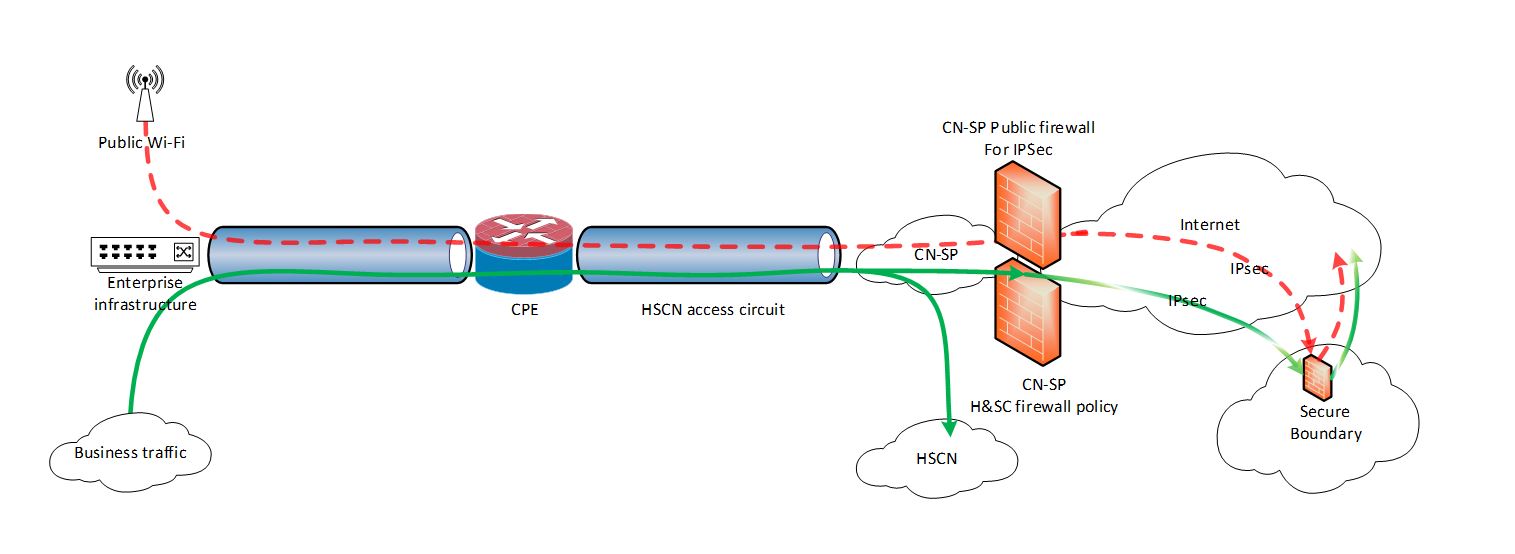
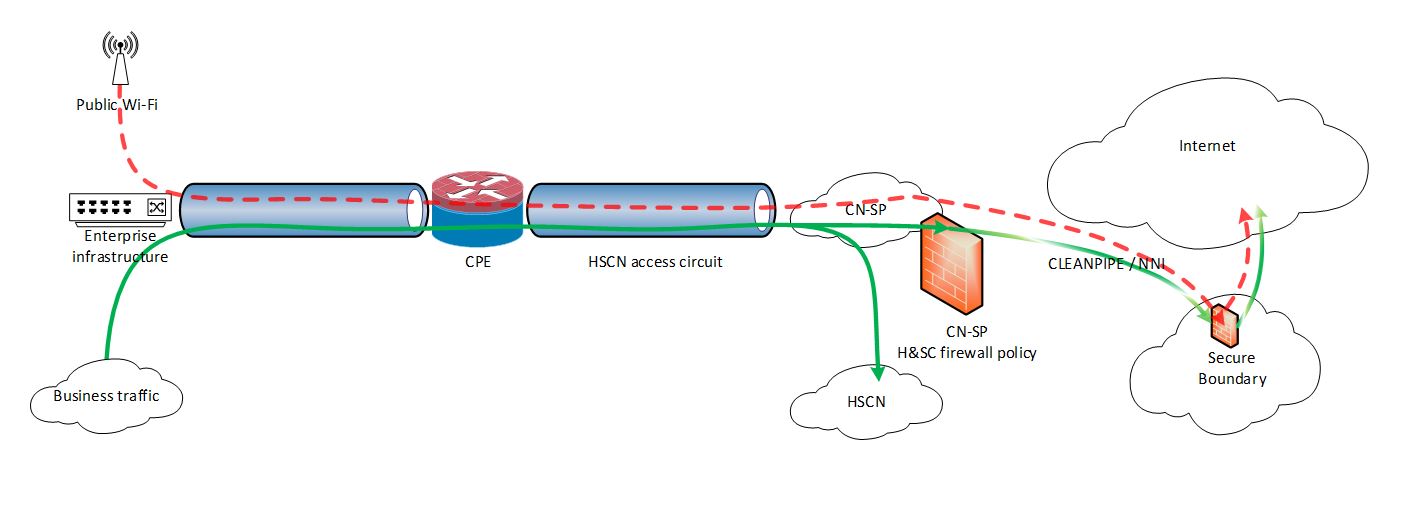
Public Wi-Fi and HSCN business traffic can be routed over the same HSCN Access circuits and break out to the internet at the Consumer Network Service Provider (CNSP) perimeter, subject to the below conditions being met.

An alternative approved option would be that Public Wi-Fi traffic may, by arrangement, be sent to the NHS Digital Secure Boundary service.
Control and protection between the CNSP and the NHS Secure boundary service would depend on how the CNSP has achieved connectivity to Secure Boundary. (Using IPsec tunnels (Fig2) , or using Cleanpipe direct connectivity to Google cloud (Fig3)) – Guidance on the connectivity options for NHS Secure Boundary are available on request.
Conditions
Separation
Public Wi-Fi traffic must remain logically separated from all other classes of traffic, end-to-end, from wireless access point to Internet egress. (This is including ingress into the Secure Boundary service)
The same physical equipment may be used.
Priority
Health and social care business traffic must be prioritised over Public Wi-Fi traffic, with Public Wi-Fi traffic being queued or dropped where business traffic demands all available bandwidth.
Flow Capture
Public Wi-Fi traffic is exempt from the centralised collection of IPfix data.
Content Scanning and Blocking
Public Wi-Fi traffic may, by arrangement, be sent to the NHS Digital Secure Boundary solution or it may break out to the internet at the Consumer Network Service Provider (CNSP) perimeter.
If the CNSP does not utilise Secure Boundary then it must ensure that the content is scanned and that, at a minimum, access is denied to sites on the Internet Watch Foundation blocklist.
If public wi-fi traffic is directed via NHS Secure Boundary, then the CNSP isn’t required to provide any content scanning as that will be provided by NHS Secure Boundary service. The requesting organization would need to adjust its Public Wi-Fi Acceptable usage agreement to state that the traffic is being scanned.
NHS Secure Boundary will provide basic filtering and DDos protection. But NHS digital shall not capture, intercept, decrypt or analyse traffic for Public Wifi.
Policy and guidance
The existing policies and guidance for Public Networks for NHS Wi-Fi remain in force:
NHS Wi-Fi technical and security policies and guidelines
Traffic separation forms part of the network boundary protection that health and social care organisations should be implementing, details of which can be found within the following NCSC guidance for Network security and preventing lateral movement:
National Cyber Security Centre - 10 steps to cyber security
National Cyber Security Centre - Preventing lateral movement
Last edited: 23 February 2022 12:48 pm